Security is always been a key factor for every business and organization, where it doesn’t matter what kind of business people run or what kind of product an organization creates. It is more important to have a secure place to run a business or for the creation of any product. The IT industry is growing towards a new edge where enterprises compete to be the best. But still, there are some cases where attention is needed and action at the right move needs to be done before anything unethical happens. ZTNA is the solution to these problems. How? Let’s see!
Introduction
Today various enterprises are working on the cloud and technologies that provide various cloud services to their users and employees to have a great working experience. But as we know, it is difficult to find whether the requested user is trustworthy or not because cyber-attacks are increasing daily, we know that intruders always have their eyes on confidential data. For enterprise data security, it is important to understand that data is granted to authorized home users or employees instead of fake ones. It’s difficult to have safe transactions if any insider attack generates. Zero trust network access is the solution to this problem.
Gartner said that Zero trust network access (ZTNA) is a product or service that creates an identity and context-based, logical access boundary around an application or set of applications. The applications are hidden from discovery, and access is restricted via a trusted broker to a set of named entities.[1]
What is ZTNA
Zero trust network access also called software-defined perimeter, is a combination of technologies and functionalities that provides secure remote access to internal applications and services. Zero trust network access enables remote users to have secure connectivity without exposing the details of the private application which are running on the internet. The applications and data will be hidden from other users, as only verified and authorized users will get access to the respective application and data that are specified by the trust broker.
Gartner views ZTNA technology as an important organizational step toward increasing the maturity of the enterprise zero-trust program, and it will appeal to organizations looking for more flexible and responsive ways to connect and collaborate with their digital business ecosystems, remote workers, and partners.[1]
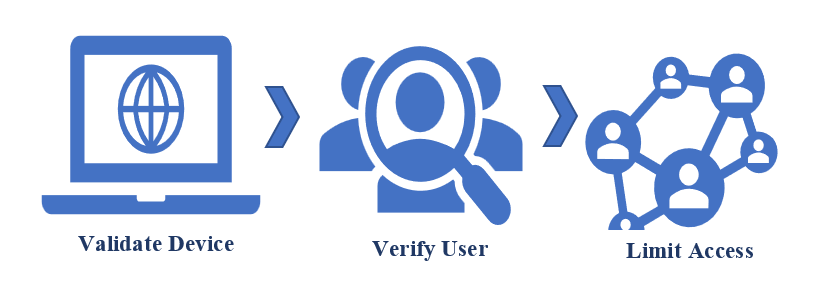
Fig.: Zero Trust Security
Why do we need ZTNA?
Cyberattacks are increasing daily and are barely hard to detect and manage with traditional terminologies. As off now insider threats are being culprits in this new era, so it’s become more important to have a precise prevention technique. ZTNA offers several terms and ideologies that help enterprises to have a secure workplace where the user or employee can do their work but with limited authority provided by the technical broker.
The ZTNA market has continued to mature and grow at a rapid pace, Gartner captured a 60% YoY growth rate for ZTNA as it augments traditional technologies for application access and removes the excessive trust once required to allow employees and users to connect and collaborate. Security and risk management leaders should pilot ZTNA projects as part of an SSE strategy or to rapidly expand remote access.[2]
ZTNA initiates significant benefits in user experience, adaptability, scalability, agility, and contentment of policy management. It fills the gaps in virtual private network access, whether sometimes VPNs struggle to fit in with the cloud network perimeters. ZTNA is an identity context-based model that uses a multifactor authentication process to verify the user or devices to establish a secure connection and provides secure access to private applications or resources based on user identity.
Architectural Concept of ZTNA
Zero-trust architecture is a security mechanism that provides zero-trust principles and protocols that support network attack prevention, restrict lateral movements of threats and, reduce the risk of a data breach. It changes the traditional castle and moat model terminologies that are been used for decades. This architectural approach supports the ‘Never Trust, Always Verify’ ideology, whether it will continuously check for the verification credentials and limits the user access after authenticating the respective user or the device which ultimately eliminates the chances of inside or outside data fraud. Zero trust exchange securely connects applications to applications, users to applications, and devices. It uses the business policies and context to have a secure and reliable connection with the right application or user. ZTNA will appeal to organizations looking for more flexible and responsive ways to connect and collaborate with their digital business ecosystems, remote workers, and partners.[2] There are some principles of zero-trust architecture that are being used in several networking and cloud terminologies to achieve a secure environment.
1) ZTNA performs isolation while granting permission to users or employees around the globe so that threats will be prevented before any damage happens and reduces risks on the network.
2)ZTNA enables outbound-only connections, here the application and resources will be visible to only authorized users or employees, and the network and application infrastructure will be made hidden from unauthorized users or employees.
3)ZTNA provides micro-segmentation, that will prevent overly permissive privileged and significantly reduce the overall attack possibilities while working on the network and cloud applications.
4)ZTNA supports a user-to-application model instead of the traditional network security model, it also enables multifactor authentication for granting secure access privileges.
Types of ZTNA
Gartner has described two main categories of ZTNA that are being used around the globe for better performance.
1)Endpoint-initiated ZTNA
Here the agent who is installed on an endpoint will communicate with the controller so that the user’s identity gets authenticated and privileges will be granted only to the authorized users. The controller will keep provisioning the connectivity after authenticating the user or employee which reduces the chances of risks.
2)Service-initiated ZTNA
Here the broker will manage the overall connectivity between the user and applications. There is no need for the endpoint agent because it supports the outbound connections and makes it useful for securing unmanaged resources as well as grants privileges to the users or employees. Some service-initiated ZTNA supports browser-based access for web applications.
Benefits of ZTNA
1)Peerless security
It provides peerless security to users and enterprises by making network devices and application infrastructure invisible to unauthorized users due to these qualities users can securely use the functionalities of the system. It improves the agility, flexibility, and scalability of the system.
2)Prevents insider threats
Zero trust will provide threat prevention against insider attacks, as it will grant permissions to only valid users and always be verified by the respective trust broker for approval. It will help protect confidential data from attackers searching for an appropriate phase to affect the system.
3)Restrict lateral movement
It will make sure that external users or devices never get entry into the enterprise network and application by ensuring that only authorized users can take the privilege to use the validated applications and services. Enforcing granular access policies can restrict lateral movements which reduces uncertain data leaks.
4)Secure control and visibility
It will make sure that excessive privileges are not granted to every user or employee who has minimal work to do on the system, it always ensures that application or services controls and visibility are enabled to only those users or employees who had requested it and allow them to use the services for granted schedule.
5)Superior productivity
It gives superior productivity by supporting micro-segmentation, significantly reducing the overall attack possibilities while working on the network and cloud applications. It protects on-premises and cloud-based services from unauthorized users to have a secure transaction or communication over the internet.
6)Multifactor authentication
Zero trust network access provides multifactor authentication which has been used to ensure valid user verification. Whenever a user or employee generates a request for any services or resources, it will ensure that all the verification activities should be done before permitting the use of the specific services and resources.
7)Enhanced user experience
It enhances performance and decreases uncertainty by approving only valid users and resources to have a secure user experience. Granular visibility and control policies enable the secure right of entry to internet appliances through a global network infrastructure that optimizes high capacity and high availability.
[1] https://www.gartner.com/en/information-technology/glossary/zero-trust-network-access-ztna-#:~:text=Zero%20trust%20network%20access%20(ZTNA)%20is%20a%20product%20or%20service,a%20set%20of%20named%20entities.
[2] https://www.gartner.com/doc/reprints?id=1-297PK28V&ct=220222&st=sb